Google has recently identified a dangerous security flaw in its Chrome browser that hackers are actively using to attack unsuspecting users. This type of flaw is known as a “zero-day vulnerability,” meaning it was discovered by bad actors before the company had a chance to fix it. The specific weakness lies in Chrome’s Visuals component, […]
On July 22, 2025, the U.S. government issued an urgent warning after discovering that foreign hackers had found a way to break into Microsoft SharePoint, a popular tool used by many businesses and government agencies to share documents and collaborate online. The Cybersecurity and Infrastructure Security Agency (CISA), which helps protect the country from cyberattacks, […]
Cybersecurity experts have uncovered a sprawling scam operation involving more than 17,000 fabricated news websites, operating across some 50 countries. This criminal network—referred to as “BaitTrap”—specializes in luring unsuspecting individuals into investment fraud schemes, cleverly disguised behind the façade of legitimate news outlets like CNN, BBC, and CNBC. The scam begins with professional-looking fake news […]
Hackers have stepped up a new phishing method that uses malicious PDF attachments to impersonate well-known companies like Microsoft and DocuSign. These fake PDFs encourage recipients to call phone numbers controlled by the attackers, pretending to be customer support representatives. This technique, called callback phishing or Telephone-Oriented Attack Delivery (TOAD), is becoming increasingly common. During […]
Cybercriminals are using fake identities and websites to trick people in the cryptocurrency community into downloading harmful software. Disguising themselves as legitimate AI, gaming, and Web3 companies, these attackers have created an elaborate scam that targets both Windows and macOS users. Their goal is to steal valuable data and drain digital wallets. The operation begins […]
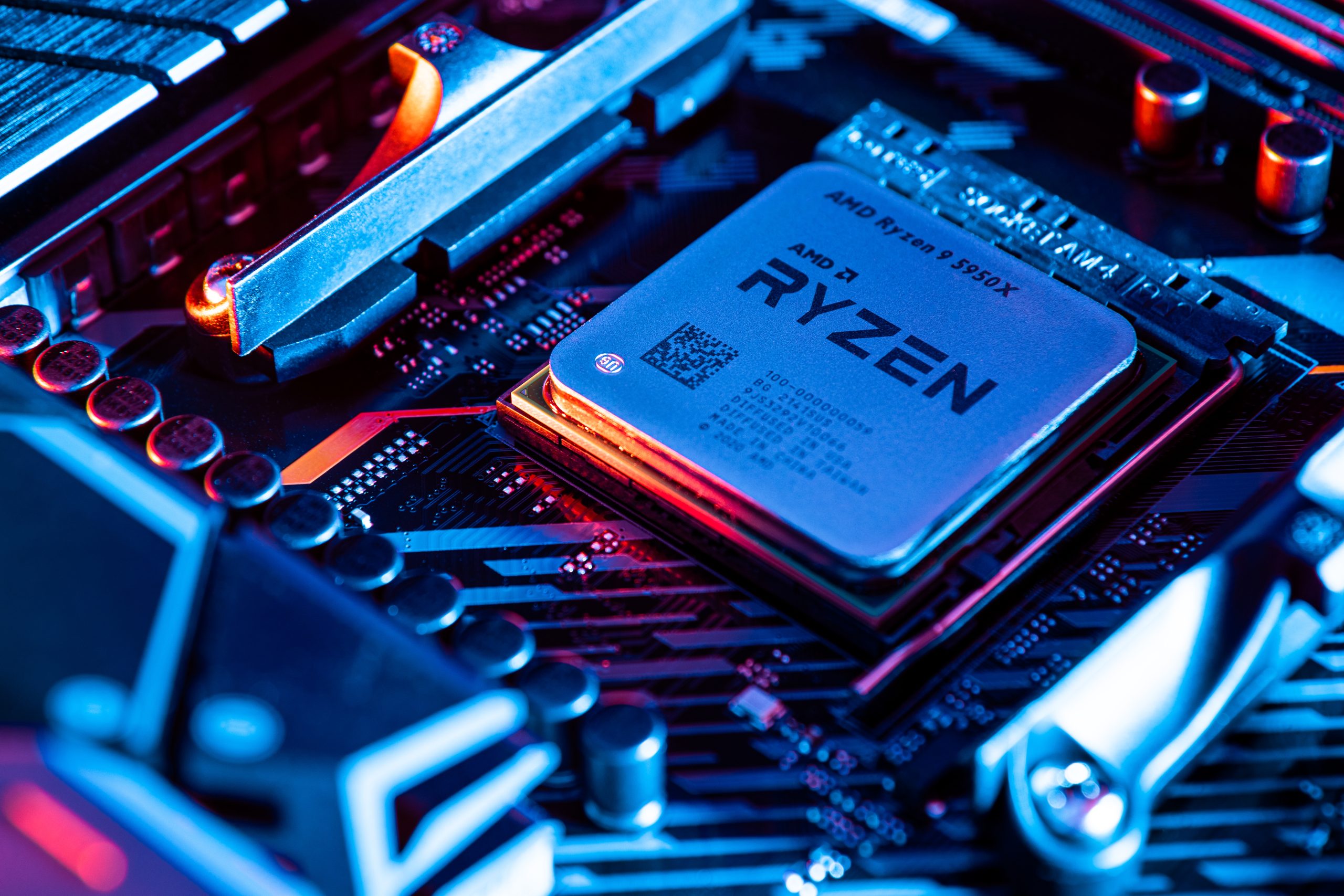
AMD has issued a warning about a newly discovered class of microarchitectural vulnerabilities, dubbed Transient Scheduler Attacks (TSA), that affect a broad range of its processors, including desktop, mobile, and server chips. These flaws arise from speculative scheduling behavior within the CPU, where timing differences during instruction execution can allow attackers to infer sensitive data […]
Taiwan’s National Security Bureau (NSB) has issued a warning regarding several popular Chinese-developed mobile applications, including RedNote (Xiaohongshu), Weibo, TikTok, WeChat, and Baidu Cloud. The NSB’s advisory highlights concerns over excessive data collection and the transmission of personal information to servers located in China, raising significant privacy and security issues for users. Following a comprehensive […]
A sophisticated cyberattack campaign is targeting Microsoft Exchange servers by quietly injecting malicious code into their login pages. By modifying the Outlook Web Access (OWA) interface, attackers can secretly log every keystroke users enter—including usernames and passwords—as they attempt to sign in. This method doesn’t rely on phishing emails or fake websites. Instead, it manipulates […]
A staggering 16 billion login credentials have been compiled and are now circulating online, representing one of the largest leaks of its kind. This isn’t the result of a single breach, but rather a massive collection of usernames and passwords stolen over the years through countless cyberattacks, phishing campaigns, and data dumps. The data spans […]
A team of cybersecurity researchers from AppOmni recently identified more than 20 configuration-related vulnerabilities in Salesforce Industry Cloud—Salesforce’s low-code platform for industries like healthcare, finance, and telecom. While these platforms streamline development, improper configurations can expose sensitive data and create serious security gaps The risks span key components such as FlexCards, Data Mappers, Integration Procedures […]