The Latest in Tech, Cloud, and Security
Deep Thoughts & Data Dumps:
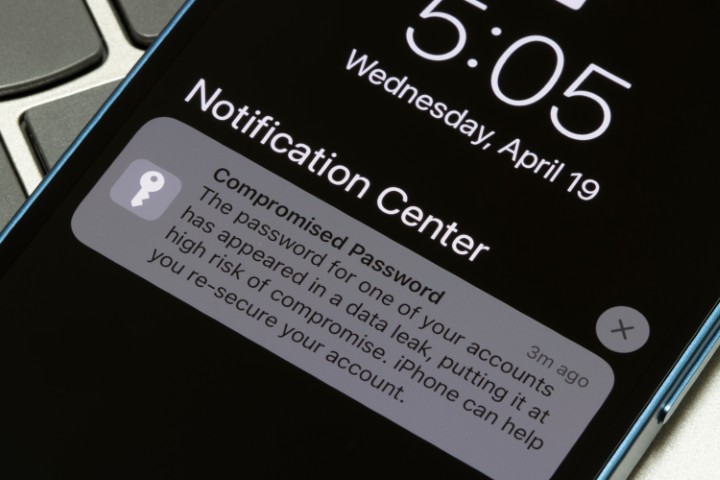
Apple has released new security updates specifically for older iPhones and iPads to fix dangerous...
Cybersecurity researchers have uncovered a new wave of attacks in which threat actors are exploiting...
Meta has announced plans to discontinue end-to-end encryption for Instagram’s direct messaging...
Security researchers have identified serious vulnerabilities in Anthropic’s Claude Code tool that...
Cybersecurity researchers have discovered a new phishing toolkit called Starkiller that helps...
Security researchers have discovered a powerful iPhone hacking toolkit that may be used by espionage...
Microsoft has warned about a phishing campaign that primarily targets government and public-sector...
A recent wave of hacktivist activity has resulted in 149 distributed denial-of-service (DDoS)...
A recent cybersecurity study has revealed serious vulnerabilities in several widely used cloud-based...